Documentation Index
Fetch the complete documentation index at: https://docs.superform.xyz/llms.txt
Use this file to discover all available pages before exploring further.
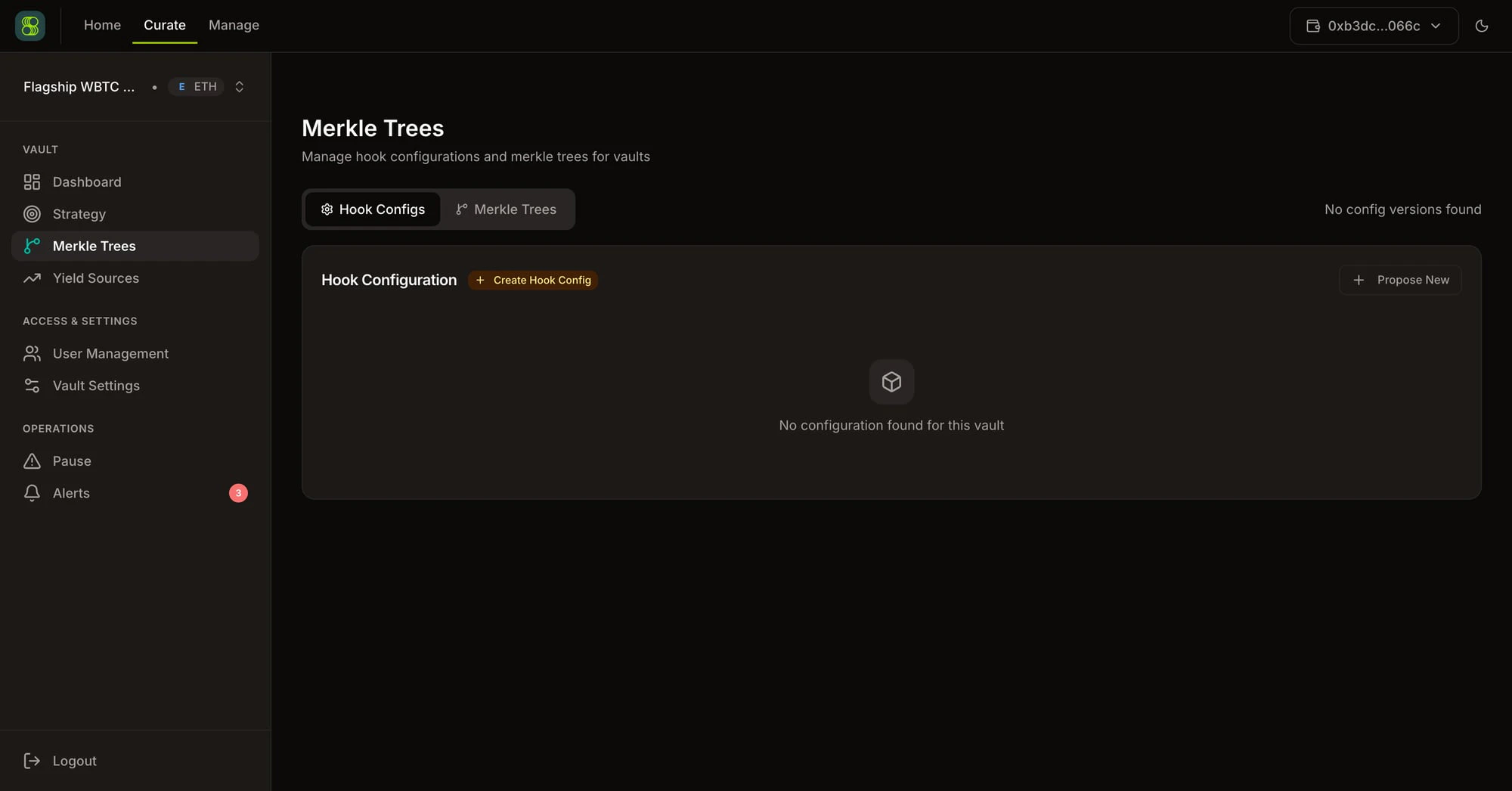
Tab 1: Hook Configs
Version History
Each vault maintains a history of hook configuration versions. The active version is highlighted. Previous versions are read-only for audit purposes.Creating a Config
Click Create New Config. For each hook to authorize:- Select Hook — from the global Hook Registry (
GET /api/v1/registry/hooks) - Set Parameters — for each
inspectParamdefined by the hook:yield_sourceref → yield source addresstokenref → ERC-20 token addressoracleref → oracle addressothers→ freeform hex value
Activating a Config
Click Activate on a config version. Only one version is active at a time. The active config is used for the next tree generation.Tab 2: Merkle Trees
Generated trees for the vault, showing:| Field | Description |
|---|---|
| Root Hash | 32-byte merkle root |
| Leaf Count | Number of authorized (hook, params) combinations |
| Config Hash | Hash of the source config version |
| Is Current | Whether this root is active onchain |
SuperVaults use two merkle roots for hook authorization: a governance-controlled global hooks root and a manager-proposed strategy hooks root. Both flow through the aggregator’s hook-root timelock, which defaults to 15 minutes and can be updated by governance. A hook must be included in either root to execute.
Generating a Tree
Click Generate Merkle Tree. Erebor starts an async job:- Polling uses exponential backoff: 2s → 4s → 8s → 15s
409 Conflict= generation already in progress- Job status:
pending→running→completed/failed
Syncing to Chain
After generation, click Sync to Chain. Erebor evaluates onchain state and returns the required action:| Sync Action | Description |
|---|---|
in_sync | On-chain root matches. No action needed. |
needs_generation | No tree exists for the active config. |
propose | Tree ready. Sign and submit root proposal (starts timelock). |
pending_timelock | Root proposed. Waiting for timelock expiry. Shows effectiveTime. |
execute | Timelock expired. Sign to activate the new root onchain. |
Keepers cannot execute against yield sources until the merkle root is synced onchain. A pending timelock means your authorization changes are queued but not yet active.
Publishing the Tree
Once a tree is generated, primary managers can publish it to make the full proof set available to integrators, keepers, and frontends without requiring Erebor authentication. Navigate to the Merkle Trees tab and locate the active tree — the one currently synced onchain. Click Publish on that tree to trigger an async publish job that uploads the complete proof artifact to a public S3 URL. Only the active tree can be published. Publishing a tree that is not the current active tree is not permitted.Publishing is separate from syncing. Sync updates the onchain root; publish makes the off-chain proof artifact publicly accessible. Both steps are needed before external consumers can verify and use the proofs.
completed:
Merkle Proofs
Proofs for each leaf are available viaGET /api/v1/merkle/proofs?vault_address={}&chain_id={}. Use these for programmatic validation or custom keeper implementations.
All Merkle Endpoints
| Endpoint | Method | Description |
|---|---|---|
/api/v1/merkle/configs/versions | GET | Config version history |
/api/v1/merkle/configs/version | GET | Single version by number |
/api/v1/merkle/configs/active | GET | Active config |
/api/v1/merkle/configs | POST | Create new config |
/api/v1/merkle/configs/activate | PUT | Activate a version |
/api/v1/merkle/trees | GET | All trees for vault |
/api/v1/merkle/proofs | GET | All leaf proofs |
/api/v1/merkle/generate | POST | Start generation job |
/api/v1/merkle/jobs/{id} | GET | Poll job status |
/api/v1/merkle/jobs | GET | Recent jobs list |
/api/v1/merkle/sync | GET | Sync status and required action |
/api/v1/merkle/publish | POST | Publish active tree (primary manager only) |
/api/v1/merkle/publish/jobs/{id} | GET | Poll publish job status |
/api/v1/merkle/published/{chain_id}/{vault} | GET | Public — get published tree metadata |